(Headline USA) China could become the next global cyber superpower if its technological advancements continue, according to several experts who testified before Congress this week.
One expert, Winnona DeSombre, a research fellow for the Atlantic Council think tank, argued China’s “offensive cyber capabilities” now “rival” the U.S.’s.
“Its operations demonstrate clear development of asymmetric capabilities that enable it to achieve strategic goals, and its cyber defensive capabilities are robust,” she said.
“The Chinese Communist Party wants China to become a ‘cyber superpower’ and is well on its way to achieving that goal.”
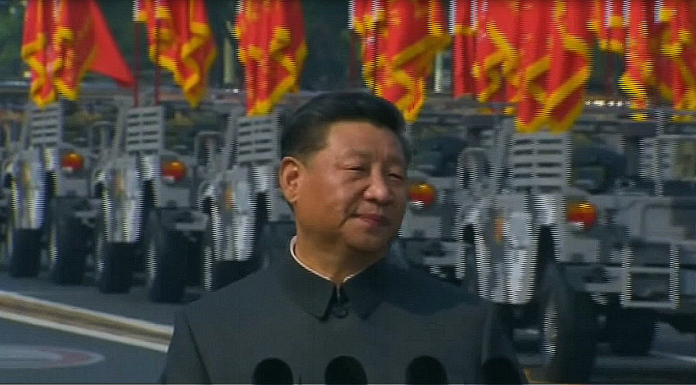
The Chinese Communist Party began focusing its operations on information and cybersecurity in 2015, after dictator Xi Jinping overhauled China’s military, the People’s Liberation Army.
One of China’s strategies has been to hack into the U.S.’s cyber infrastructure and steal information, which they have used to develop “information technologies, including artificial intelligence, big data, and cloud computing,” according to Heritage Foundation expert Dean Cheng.
“The result has been essentially a military-scientific revolution, requiring new operational forms and theories, and potentially further alterations of the PLA’s organization,” he said.
China has also created its own education system to create talent for cybersecurity exploitation and strengthen its operations, the experts said. For example, the CCP unveiled a standardized cybersecurity curriculum that is being used in university degree programs.
“Over the next decade, China’s cyber capabilities are poised to blossom as universities graduate more well-educated cybersecurity degree holders and as research progresses,” said Dakota Cary, a research analyst for the think tank Center for Security and Emerging Technology.
In one of these university classes, a Chinese professor at Southeast University held a “capture-the-flag” competition for his students, wherein they would compete by attempting to hack into a U.S. Department of Defense contractor system, he added.
“Unlike normal capture-the-flag competitions where participants hack other teams for points, the professor offered students a real-world opportunity to earn points and gain prestige by attempting to access the network of a U.S. Department of Defense contractor,” he said.